Personal Information Backup - Twitter, Gmail Contacts, Google Calendar, Reader
Make a New Year's Resolution to start backing up your data regularly. Not just local files, but even data from the cloud. Here's how to backup your data from a few of the most common online services. More importantly, I've also included instructions on how to restore from that backup.
How to backup?
Copy this URL to a new browser window.
https://twitter.com/statuses/user_timeline/USERNAME.xml?count=10000
Then replace the string USERNAME with your actual Twitter username. Press enter to start downloading. If your browser does not prompt you with a file download box, but instead opens the file showing a bunch of text, choose File > Save As to save your backup to a secure location.
How to restore?
You cannot restore this data into Twitter (neither to your own account, nor to a different account.) But you will have access to your witticisms and interesting web links that you posted to amuse your friends. Do with it as you please.
Gmail Messages
How to backup?
Use an IMAP client such as Mail.app on the Mac, or Thunderbird on any platform. Make sure it's configured to download and cache every email and every attachment.
How to restore?
You can access your messages from these programs even if Gmail is down. If you need to transfer messages to another account, add that new account in the same program as a new IMAP account, then drag-and-drop messages from your old account to your new account to transfer them there.
Gmail Contacts
How to backup?
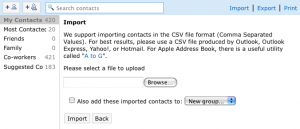
Login to your Gmail / Google Apps email account, then open the Contact Manager. Click on the Export button in the top-right corner. For maximum compatibility with other applications, choose the third option for data format, vCard format. (It's a standard format for contact information exchange.)
How to restore?
The vCard format is fairly standard. Gmail itself can read back the same file without trouble. To import into Mac OS X Address Book, simple double-click the .vcf file and let the import proceed. Microsoft Outlook also supports importing addresses from vCard files.
Google Calendar
How to backup?
Google Calendar publishes feeds of your calendar in the iCal format. If you save this feed to a file, you can use it as a backup. On the left side of your main calendar, there is a list labeled "My Calendars". For each calendar that you want to backup, click on the little downward-pointing arrow next to the calendar name, and select "Calendar Settings".
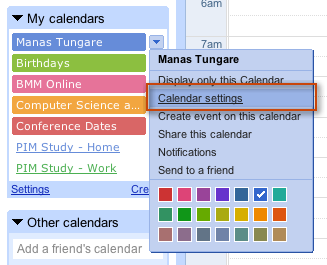
On the Settings page, under Calendar Details, locate the section labeled "Private Address". Click on the button labeled ICAL and copy the URL there. Open a new browser window and paste the URL there. This will start downloading a file; save it to a safe location -- this is your calendar backup. Lather, rinse, repeat for each calendar you want to backup.
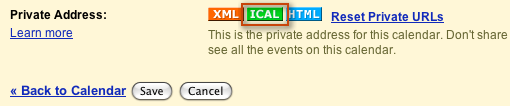
How to restore?
The iCalendar format (also abbreviated as iCal or .ics) is a standard calendar format. You can import the backed up calendar file into Google Calendar, Apple iCal or Microsoft Outlook simply by opening it.
Google Reader
How to backup?
Login to Google Reader, then come back here and click on this link: Export Google Reader subscriptions as OPML. Save the file that your browser will prompt you to download. This is your backup.
How to restore?
Google Reader and lots of other feed readers know how to import OPML files. In case of Google Reader, go to Settings > Import/Export to import it back. For desktop software, try looking for an "Import from OPML" menu item somewhere.
Need instructions for more services? Write a comment and I'll try to provide them.
Book-as-Blog: Encouraging Reading by Posting a Chapter at a Time
I realized I haven't picked up a book in weeks, (non-academic book, that is), but I've read more than my fair share of blogs in that same time. I wonder if part of the reason is the longer time commitment required by a book. This prevents it from being read quickly and keeps it forever on my wish list. If so, then how about a service that breaks down books into blog-post-sized chunks and publishes them every few days?
The idea is inspired by, -- nay, stolen from -- Kevin Kelly, who is reissuing his 10-yr old book as a blog (hat-tip to Seth Godin's post on the topic). His reasons are different, though. The book is out-of-print, and is already available as a downloadable PDF from his web site. Making it available as a blog is just another way of spreading his ideas wider, which is a great idea.
But apart from that, I like the idea of chopping up a book into chapter-sized chunks and making them available to readers one at a time. Not for any economic reasons, but because attentional resources are so scarce these days. A few times during the day, I have some free time which I use to read a few blog posts. If I ever thought about picking up a book during these breaks, I wouldn't do it, simply because of the (arguably artificial) time commitment issues it raises in my mind. But talk about a chapter-sized, or even smaller blog post, and I'd read it.
Of course, not all book content has an affordance for this kind of splicing and dicing. If it takes several minutes for a reader to re-establish context from the last blog post, the purpose is lost. Some authors would consider their books a work of art too precious(ssss) to split it up into anything smaller. That's also the reason why bands are often reluctant to sell singles instead of entire albums (apart from the record labels preferring to sell you 9 lame tracks bundled with 1 great track for $10 instead of $1, thank you very much.) But several non-fiction books could verily adapt to such a format.
The book-as-blog need not be free (as in no charge.) Sure, charge me for it. Implementation would be easy, charge me a micropayment and give me a secret watermarked feed URL. With so much new content licensed under a Creative Commons attribution license, it's also possible to develop a web service that does this for liberally-licensed and public domain works. This is compatible with Creative Commons Attribution (BY), Attribution-ShareAlike (BY-SA), Attribution-Noncommercial (BY-NC), and Attribution Non-commercial Share-Alike (BY-NC-SA) licenses (but I'm not a lawyer, this is not legal advice, blah blah.)
Maybe something like this will finally get me back to the several-books-a-month club I used to be a member of, until I discovered this newfangled shiny thing called the Internet.
Software and the Democratization of Production
The availability of consumer software in this century has democratized the production of ... well, everything. Parts of the current creative landscape seem no different than Marxist philosophies of workers owning the means of production, with one exception: the workers aren't doing it for money, they're doing it for fun.
I recently watched Be Kind, Rewind, that's what has inspired this post — at least the spark behind it. In the movie, two video store employees recreate popular movies using a video camera when the original tapes get erased by a mysterious magnetic force. Their videos were, of course, of very low production quality, but the general idea was still valid: that amateur-grade equipment is approaching professional grade equipment.
That made me realize how easy (or at least, possible) it is to create movies with affordable software on consumer hardware. When things were still in the analog domain, you would need specialized hardware to be able to shoot on film, capture audio on expensive multi-track recording equipment, and edit it all by splicing film together. Now, all you need is a digital video camera and a general-purpose high-end computer (which, incidentally, can also be used for other tasks, so is cheap.) The barrier to entry for amateur film-makers has almost been removed.
Ditto with music production — it is possible for a musician to set up a studio in his/her basement with cheap equipment that doesn't cost an arm and a leg. The quality of recordings made with these tools is comparable to what the studios churn out.
Publishing is no longer the domain of the publishing house — Gutenberg's printing press now inhabits every single computer that has a printer attached to it. High quality design tools and cheap reproduction has made publishers out of everyone: flyers, posters, announcements, articles, books — all of them required professional assistance in the past. Newer genres such as wiki articles, blog posts and Usenet postings have been made possible by the Internet.
An entire "prosumer" grade of still cameras has made its way into the hands of millions of photographers. Shooting digitally has minimized the variable costs associated with photography, thus unshackling the amateur from budgetary constraints that professionals never had to bother about. That brings them one step closer to competing with professionals, e.g. by selling their shots as stock photos online.
As the economy turns digital, distribution is also taken care of democratically. Earlier, it would take a promoter, someone who could invest the initial millions, to take a creation to market. Today, it's as easy as uploading it to YouTube or selling it on iTunes or printing a book on Lulu or making a shirt at CafePress. If it's good, it will go viral. Simple as that.
Nowhere is this change more apparent than in the recently-concluded Presidential Election in the United States. Barack Obama is spoken of by many as the first YouTube president. Indeed, the numerous amateur videos posted by his fans to YouTube and Twitter and on their blogs played a major part in spreading the word about his ideas — in a way that pre-Internet generations could never have.
If I were an anthropologist circa 3000 AD, the last three decades would show up as a significant inflection point in a graph of human achievement and creativity.
Here's to software!
Email should have Expiration Dates
The entire idea behind this blog post has been summed up in the title, so all I need to do now is to explain why I think email should have expiration dates, and how that would make personal information management better.
Email, as we all know, started off as a way of sending short messages to colleagues within a department. It has since evolved into a monster of a tool that does everything it was never designed to do. The paradox is that it is exactly the kinds of messages that email was designed to handle that cause me the most trouble these days.
- I often receive email from my friends about meeting up for lunch. This is important, but only for that particular day (and that too, if I receive it before lunch time).
- My research collaborators send me email when a paper submission deadline is near, with the draft attached to it. Those emails are not nearly as important after the deadline.
- My friends and I exchange travel plans over email, but is it as useful after the trip is done?
These are the kinds of messages I'm talking about: important but time-sensitive. Then there are others which are not really important, but simply one-time notifications that I can take action on and then forget ("bill is due in 2 days", "X added you as a friend", "your order was received", "your package has shipped", "free donuts in break room", "we are not meeting today", etc.)
Why do they linger on in my mailbox for years? They become indistinguishable from the really important email that I need to save for years, such as some very interesting and intelligent discussions I have had with others. Note that I'm not including spam in this discussion, because in my opinion, there are adequate spam-filtering tools circa 2008 that perform well enough for most users for the most part with an acceptable false positive rate. Not perfect, but acceptable.
The Keeping Problem
Email is no longer ephemeral -- people hold on to their email for years. This is what results in the Keeping Problem in Personal Information Management: there is so much of information coming at us that we don't want to spend the time to decide what to keep and what to trash, so we end up keeping all of it. We hope we never have to do spring cleaning, and instead rely on search to find what we want.
Filing is not the answer
Many people file and tag their email, but the question is, is the cost of doing so (time as well as attention) worth the payoff at the end? Consider the two alternatives: spending 10 minutes each day filing your email, versus spending an hour a month looking for that one email. Pretty soon, the second alternative starts looking better while swimming in a sea of email with no signs of abating.
Same needle, bigger haystack
The bigger the haystack grows, the harder it is to find the needle. The solution is to reduce the size of the haystack. Automatically. Most other solutions empower the user to filter, sort, file, tag and do other sorts of things to their email that do not scale very well. That's where Email Expiration Dates come into play. For it to work, they need to be (1) defined and (2) honored.
Defining an Email Expiration Tag
Email expiration tags can be defined in several ways by several entities that handle the email message at some point of time in transit.
- By the sender of that email who cares about the recipients;
- By the email client (MUA) used by the sender, automatically inferring from certain common-sense words; e.g. subject contains lunch and body is less than 100 bytes;
- By the email server software that intelligently tags email based on common patterns seen across multiple users;
- By the recipient's email client, based on heuristics;
- By the recipient's email client, based on a user-defined rule set;
- Or explicitly by the recipient in a spring cleaning session.
Honoring an Email Expiration Tag : Fully standards-compliant
RFC 822 allows custom tags (Sec. 4.7.5). These are commonly referred to as X- headers, since the specification requires that all such tags be prefixed with "X-". Many applications built on email make use of such tags: mailing lists use the X-List-* headers to specify the list name, subscribe URL and unsubscribe URL in a mail message. Spam filtering software such as SpamAssassin assigns a score to each email, saved as an X- header. Mail clients are free to interpret these tags as they see fit.
An expired email will not be automatically deleted if the user does not want it to be. This is important for archival purposes and to satisfy the stringent reporting requirements of the Sarbanes-Oxley Act. But now the user can make a one-button choice about whether or not expired emails be deleted, archived, moved away or kept around.
With help from legitimate bulk email senders (not spammers)
Bulk mail such as Facebook notifications could have expiration dates set to "one week after receipt". Bill reminders could set the expiration date to be "2 days past deadline" (and then send another notification if payment is not received by then.) Donut announcements could expire at the end of the day. Talk announcements could expire at the end of the talk.
Fixing the post-vacation blues
Returning from a vacation is no longer refreshing, as we are thinking about the sheer volume of email we need to process once we get home. If I was on vacation when the donuts were on the table, I should not be bothered about it when I return. Go away! If it's an invitation to a talk that happened while I was away, I don't need to hear about it now.
What will it take for adoption?
Defining a standard is no use if it isn't used. The best way for such a solution to be adopted is for a major email provider implement it themselves, perhaps in a limited beta? On the interface side, this requires two additions: one for sending, one for processing received messages. The widget at the sender's end is simply a calendar picker, or a drop-down with relative dates ("tomorrow", "next week", etc.) At the receiving end, it's a three-way radio button that lets users "Delete", "Archive" or "Leave alone" expired messages.
Till then, it's back to manual spring cleaning. Oh well.
Acknowledgments: I have had several stimulating discussions with my advisor, Manuel Pérez-Quiñones, and my colleague, Pardha Pyla, about our respective email filing strategies, (that mostly began as venting sessions). This idea no doubt borrows from my analysis and conclusions based on some of those conversations.
HOWTO Obtain metadata for a book given its ISBN using Amazon Web Services in PHP
This is a quick snippet I put together for an academic project. To be able to write this, I had to go through several documentation resources, for what is essentially a single web service method call. I figured it would help if I shared my PHP code.